Overview
Implementing complex, secure, end-to-end communications from an IoT device can be difficult, time-consuming and expensive.
Although there are now good ICs and modules available for a range of communications technologies (such as 3G/4G/5G/NB-IoT, WiFi, BLE, Zigbee or LoRA), these normally have very basic link-layer security and will secure communications only between two interfaces of the same type. In a typical IoT scenario, data travelling from a device to its destination (typically a cloud-based server) has to pass through multiple communications technologies, with bridge devices converting from wireless to wired communications or changing network protocols.
To keep data secure across multiple communications technologies and protocols then requires an application-level protocol to be used on top of each communications technology. For example, the TLS cryptographic communications protocol could be used to protect an MQTT message stream. TLS is a commonly used protocol, however it is a heavy-weight IT protocol and is not ideal for wireless devices both in terms of bandwidth use as well as power consumption. It is also not very scalable or very suitable for device-to-device communications.
To secure data from an IoT device, it is also necessary to protect the cryptographic keys and certificates used. As many IoT devices are physically accessible, a high level of hardware protection is required against attackers if the data from the device is mission-critical (e.g. used in analytics) or needs to be protected (e.g. for privacy law reasons). This then leads manufacturers to have to integrate hardware security devices such as HSMs into their products.
What starts out to appear to be a relatively simple task, quickly turns into a major, time-consuming and resource-consuming project. It also requires considerable expertise to ensure the security is correct and it needs to be maintained over the lifetime of the product to ensure that it stays secure.
Accelerating our customers time to market
After working on a number of these projects, Cerberus decided to create a solution that could be used by our product manufacturing customers to avoid this pain.
Our aim was to produce a solution that is:
- Cost effective
- Easy to integrate
- Pre-configured with secrets and so avoids the need for secure manufacturing lines
- Easy to configure at installation time
- Able to support complex use-cases such as machine-to-machine and multiple data destinations as well as simple point-to-point secure links
- Capable of allowing monitoring and auditing of IoT networks and devices
- Able to help with all aspects of the IoT lifecycle such as: on-boarding; secure updates; and transferral or destruction
- Hardware-secure
Product range
We have developed “Helios” hardware system-on-modules and other components that manage secure communications and the other essential IoT functionality mentioned above.
Please note: Helios products are currently for use in our consulting projects, although we are working towards general sales in Q3 of 2021.
If you would like to discuss use of any Helios product or to arrange a demonstration or engineering samples, then please contact us.
Our product range consists of the following components (click on the component name to scroll to the relevant section) :
| Component | Purpose |
|---|---|
| System-on-modules | Supports different edge device communications technologies and protocols |
| Interface boards | Interfaces Helios modules with other equipment |
| Network bridges | Convert between different physical networks and network protocols |
| Gateways | Manage the network, process data locally and securely forwards data (e.g. to other networks or the cloud) |
Helios modules are designed to be used in conjunction with a host microcontroller or microprocessor and are not user-programmable. A simple software API is provided for the host device. They are also secure by design and include HSMs to store keys and certificates safely.
Helios modules
Helios modules provide the first step of the communication from the edge node. All modules have the same pad footprint and the same pin function, although some modules operate at 1.8V and others at 3.3V.
There are a number of models of Helios and each model may have further configurations:
| Model | Commmunications protocol | Configuration options |
|---|---|---|
| IEEE 802.15.x | BLE 5, 802.15.4 mesh | 1.8V low power, 3.3V high power, external antenna |
| LoRa | LoRaWAN | external antennae |
| Ethernet | Ethernet | Power-over-Ethernet IEEE802.3af |
Each model may also have different amounts of on-module memory that can be used for secure storage (in case communications are intermittent) and for securely updating the host processor. Each module also supports active NFC for provisioning, programming and configuration.
Click on the model name in the table above for more information.
A simple host-based API (supplied as portable ‘C’, ‘C++’, Go or Python source code) is used to control the modules and store and send data securely. Modules have a range of physical interfaces including UART, SPI, I2C and SDIF (available on high-bandwidth modules only).
Helios IEEE 802.15.x
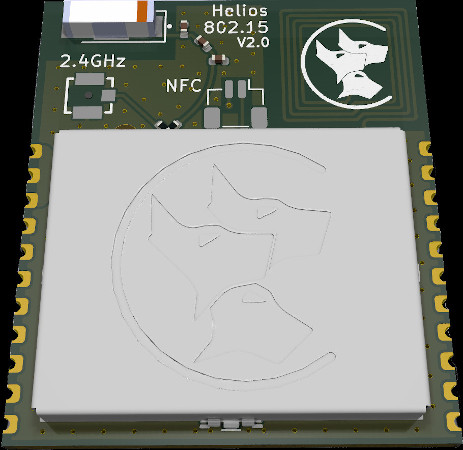
Operating at 2.4GHz, the Helios IEEE 802.15.x modules can interface to Bluetooth Low Energy (BLE) devices (including mobile devices running Helios communications software) using BLE5, as well as 802.15.4 based mesh networks.
Helios LoRa
Coming soon
Helios Ethernet
In development
Interface boards
We have developed a range of interface boards to aid with evaluation of the Helios modules and for the rapid prototyping of IoT systems and product ideas.
Break-out board
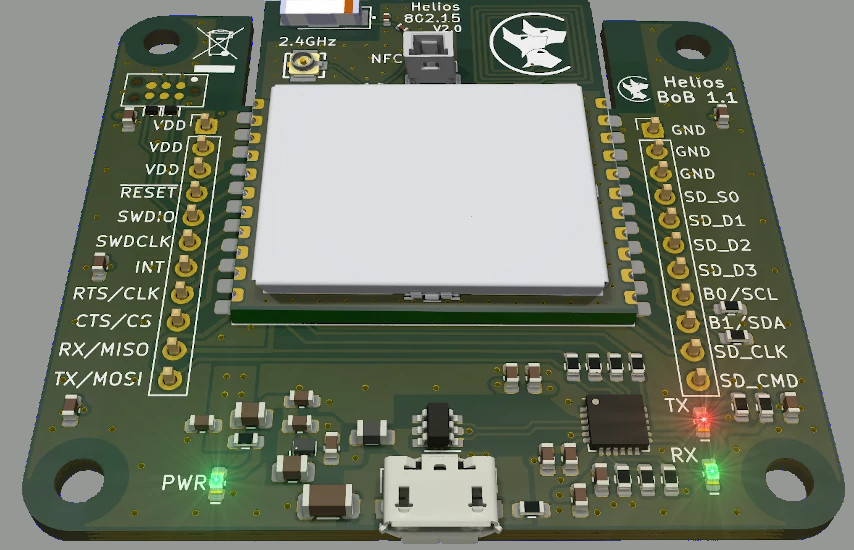
The Helios Break-out Board (BoB) breaks out the pins from a Helios module into (0.254 mm / 0.1 inch) pin headers, for easier access and use with development boards. It also provides a full-speed (12 Mbps) USB interface for interfacing to the module over a USB UART and also provides the module power.
The Helios host software can then be used to control the module and send data. Ports of the host software for Windows and Linux are currently available, in C, C++, Go and Python.

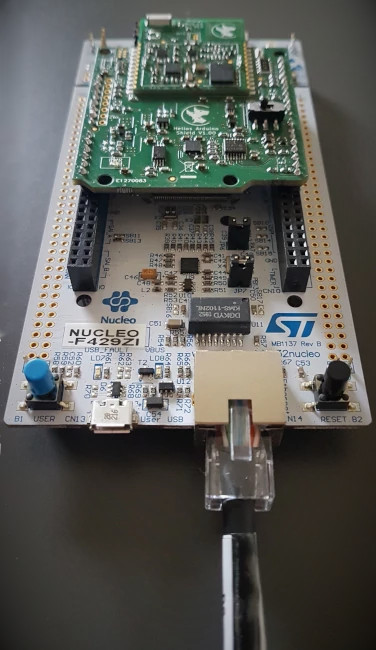
Arduino shield
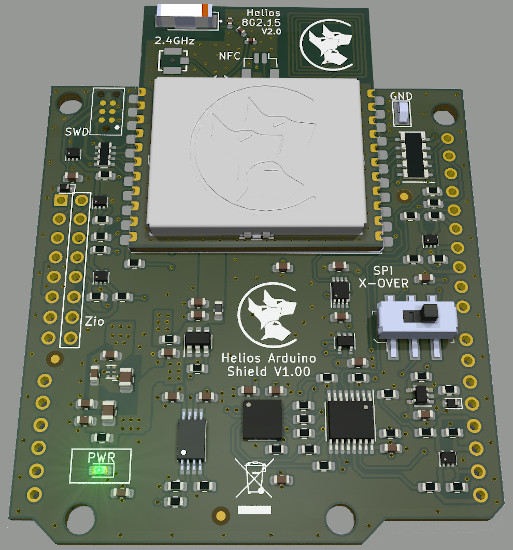
The Helios Arduino Shield (HAS) allows a Helios module to be used with any board with an Arduino R3 compatible connector. This can be either an Arduino or clone, or else development boards from a range of manufacturers. Both 5V and 3.3V interfaces are supported and automatically set the voltage based on the IOREF pin.
The HAS board supports :
- Arduino UNO R3 (and its many clones)
- Arduino DUE
- ST Nucleo development boards
- Any other 3V3 or 5V dev board with Arduino connectors (e.g. Microchip FPGA board)
The board includes support for the ST Zio extension header, present on Nucleo-144 boards, which allows for an SDIF interface to Helios modules with high-speed interfaces.
Network bridges
Network bridges allow conversion between different network technologies and protocols.
Power over Ethernet (PoE) bridge
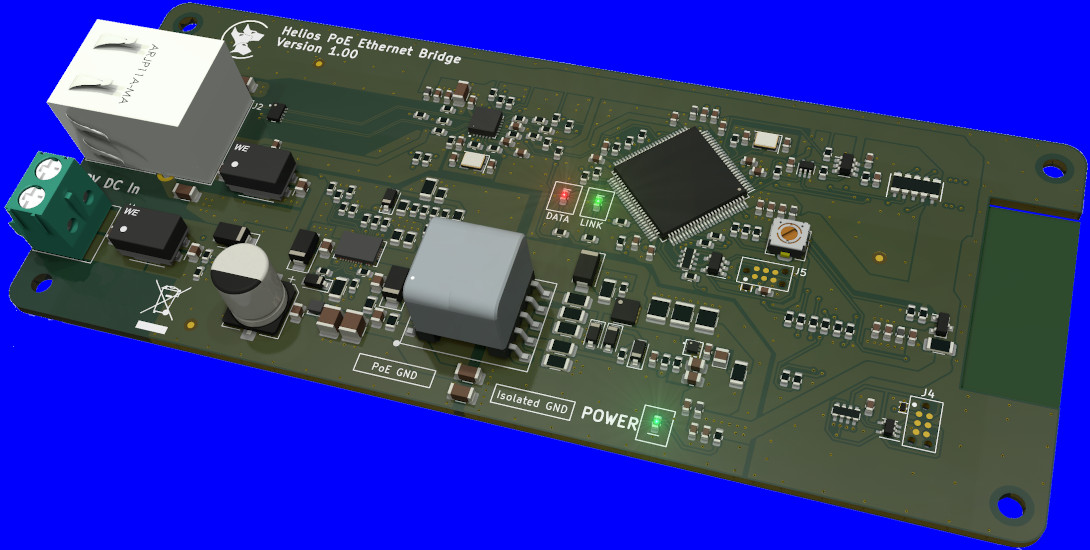
The Helios PoE bridge can be used to convert between a wireless technology and ethernet.
Current wireless options include :
- BLE
- IEEE802.15.4 mesh networks
Network gateways
Network gateways are used to :
- monitor the network
- manage remote device updates
- process data locally (with no cloud involvement)
- forward data to other networks and services (such as cloud services)
Our Gateways incorporate a Cerberus Atlas HSM running on a PCIe FPGA card to ensure data is end-to-end secure.
Software tools
Network configuration software
Helios networks can be designed using a simple graphical interface. A data-centric approach allows data channels to be created, configured, monitored and linked between devices, bridges and gateways.
The configuration software is cross-platform and runs on Windows, MacOS, Linux, iOS and Android.
Provisioning and maintenance software
Helios modules include active NFC transceivers and these can be used during manufacturing and installation stages to :
- join devices safely and securely to a network
- personalise modules for a specific product
- obtain diagnostic reports
- update firmware locally
This software is designed to run on mobile devices with NFC support.
